Android
Samsung June 2021 Security Patch Details – New Fixes [One UI/Android]

As always, Samsung launched the June 2021 One UI security patch before changing the calendar month, even ahead of the stock Android, commonly known as Google. The Galaxy S21 series was to first to grab the latest security patch, a week before this month.
Later on, the company expanded this latest security improvement package to more Galaxy devices from different segments and all of the latest and older (eligible) flagship phones have started getting it over the air in various smartphone markets.
Well, the most awaited Samsung June 2021 security bulletin has officially arrived, which includes dozens of new fixes for CVEs from Google and Samsung. At the same time, the company said that it has already fixed some exploits with the previous patches, while some are not applicable for Galaxy devices.
According to the official document, Samsung’s June 2021 security patch update brings fixes for 2 Critical (CVE-2021-0507, CVE-2021-0516), 27 High, and 5 Moderate levels of CVEs to Galaxy phones and tablets. While fixes for 9 new CVEs already included in previous updates and 4 not applicable to Samsung devices.
Samsung Android June 2021 Security Bulletin [New CVE Fixes]
Critical
CVE-2021-0507, CVE-2021-0516
High
CVE-2021-1891, CVE-2020-11284, CVE-2021-1905, CVE-2021-1915, CVE-2021-1927, CVE-2021-28663, CVE-2021-28664, CVE-2021-0495, CVE-2020-11279, CVE-2020-11273, CVE-2020-11274, CVE-2020-11285, CVE-2020-29661, CVE-2019-2219, CVE-2021-0511, CVE-2021-0521, CVE-2021-0508, CVE-2021-0509, CVE-2021-0510, CVE-2021-0520, CVE-2021-0505, CVE-2021-0506, CVE-2021-0523, CVE-2021-0504, CVE-2021-0517, CVE-2021-0522, CVE-2021-0304
Moderate
CVE-2021-1906, CVE-2021-0381, CVE-2020-0025, CVE-2021-0385, CVE-2021-0389
Already included in previous updates
CVE-2021-0492, CVE-2021-0491, CVE-2021-0493, CVE-2021-0494, CVE-2021-0497, CVE-2021-0498, CVE-2021-0489, CVE-2021-0490, CVE-2021-0496
Not applicable to Samsung devices
CVE-2021-0467, CVE-2020-11288, CVE-2020-11289, CVE-2021-1910
Samsung Android June 2021 Security Bulletin [New CVE Fixes]
Alongside Google patches, Samsung provides 19 SVE items in order to improve Galaxy device owners’ confidence in security. You can check the list below.
Note: Some of the SVE items may not be included in this package, in case these items were already included in a previous maintenance release.
- SVE-2021-20702 (CVE-2021-25410): Arbitrary file access vulnerability in CallBGProvider
- SVE-2021-20877 (CVE-2021-25413): Possible to access arbitrary content providers
- SVE-2021-20879 (CVE-2021-25414): Possible to theft or overwrite arbitrary files
- SVE-2021-21161 (CVE-2021-25407): Out of bounds write in Samsung NPU driver
- SVE-2021-20641 (CVE-2021-25417): Improper authorization in SDP SDK
- SVE-2021-20984 (CVE-2021-25412): Improper access control in genericssoservice service
- SVE-2021-20948 (CVE-2021-25409): Configure Notification settings without authorization
- SVE-2021-20178 (CVE-2021-25415): Possible remapping RKP memory as writable from EL1
- SVE-2021-20179 (CVE-2021-25416): Possible creating executable kernel page via abusing dynamic load functions
- SVE-2021-20176 (CVE-2021-25411): Vulnerable api in RKP allows attackers to write read-only kernel memory
- SVE-2021-21074 (CVE-2021-25408): Buffer overflow in Samsung NPU driver

STAY CONNECTED WITH US:
- Join SammyFans on Telegram
- Like SammyFans.com on Facebook
- Follow SammyFans on Twitter
- Get news in graphics on Instagram
- Get the latest insights through Google News
- Send us tips at – [email protected]
Android
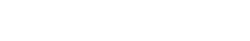
One UI 7 to bring Android 15’s secret Landroid screensaver

Android 15’s Easter Egg includes a secret Landroid screensaver mode that One UI 7 might borrow. Samsung’s next One UI iteration will be based on Android 15 OS. Core Android features such as Easter Egg will be included in Galaxy’s next major upgrade.
Debuted as a Landroid screensaver, Android 15’s Easter egg was added with the latest Beta. Google News Telegram channel’s Nail Sadykov discovered that the Easter egg game is equipped with an integrated screensaver mode.
To activate Easter Egg, head into Settings followed by About phone and Android version. Once done, tap the displayed Android version several times until you see the Android 15 bugdroid logo floating in space.
Space travel mini-game will be available to play added with Android 14. When you initially trigger the mini-game, you should have unlocked the new screensaver, tucked away under Settings → Display & Touch → Screen saver → Landroid.
After activating the screensaver, you can set your phone on your desk. Now, the phone will let you watch the Easter egg game take over in autopilot mode, as the spacecraft automatically dodges planets – it provides a better experience on a tablet placed on a dock.
AI
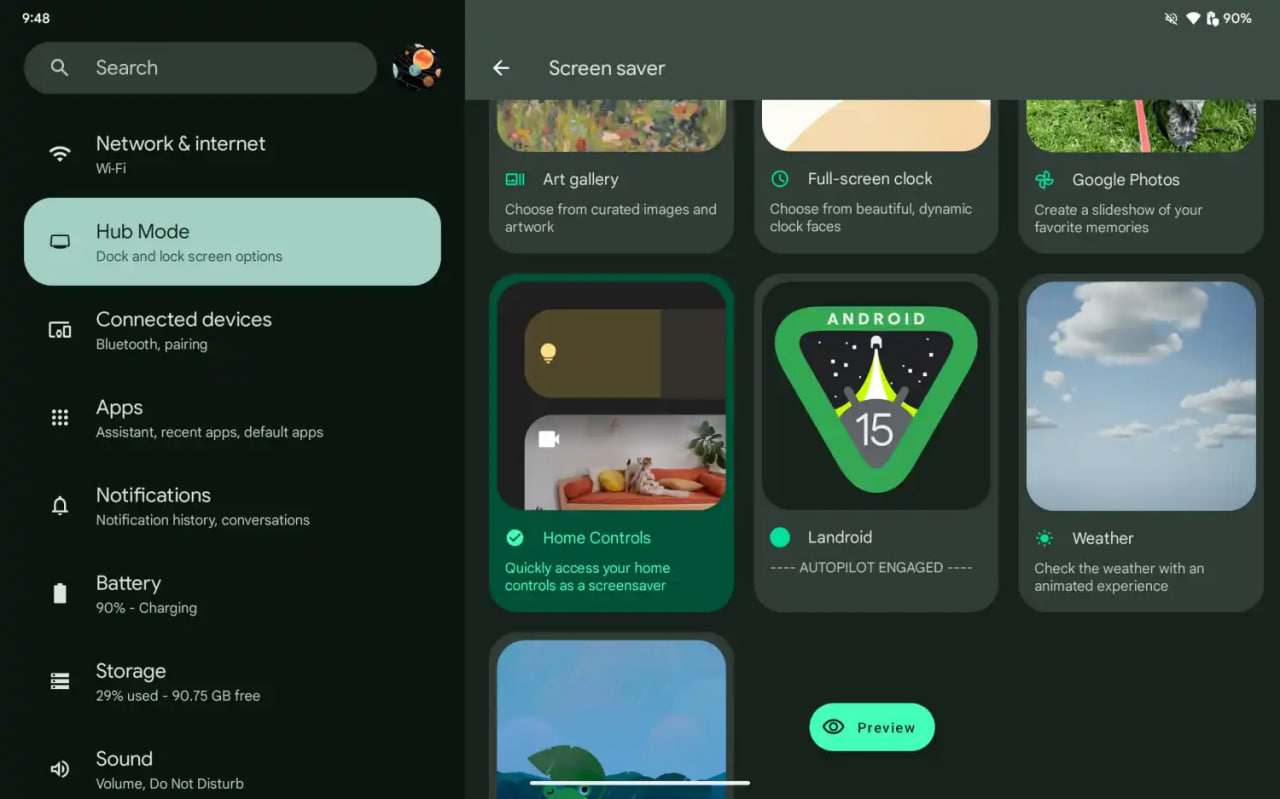
Android 15 might let you share AI-generated wallpapers

Google introduced the AI Wallpaper feature with the Pixel 8 series. The same functionality is also available in Samsung’s Galaxy S24 series thanks to Genini Nano. Now, Google is preparing to make AI-generated wallpapers sharable with Android 15.
Pixel’s ability to create AI-generated wallpapers is quite popular among users. Currently, the feature only allows users to generate stunning wallpapers and apply on the home screen and lock screen. Sharing with someone presently requires to be saved as a screenshot.
Threads user @the_husbandalorian discovered interesting evidence in the latest Beta. The company is working on a new option in Android 15 to share AI-generated wallpapers. A new share button is added on the preview screen in the wallpaper picker interface.
Post by @the_husbandalorianView on Threads
The preview will display how the wallpaper will be applied to your phone’s home or lock screen. The pencil button will allow you to refine the prompt used to create the wallpaper. Share button is all you need to share AI-generated wallpaper with others.
At present, the ability to share AI-generated wallpaper is broken. It suggests the feature is still under development and requires additional work. The next Beta might make it functional for Beta users, and we guess public availability with a Stable rollout.
AI Wallpaper in One UI 6.1
Android
Samsung Android 15 Update: One UI 7 Ineligible Devices [LIST]

Samsung is very well known for its excellent after-sales service and software support. The company announced that it will provide up to 7 years of major OS upgrades and security updates for its flagship devices, starting with the Galaxy S24 series. This is a remarkable achievement that will allow Samsung users to enjoy the latest features and security enhancements for a long time.
Not all Samsung devices will be eligible for the upcoming Android 15-based One UI 7 update, which is expected to bring several new features and improvements. Some older and lower-end models of the Galaxy A, Galaxy M, and Galaxy F series have reached the end of their software upgrade cycles, and will not receive any further OS updates.
Follow our socials → Google News, Telegram, X (formerly Twitter), Facebook
However, these devices will still receive security patches for another year, but they will miss out on the new features and benefits of One UI 7.

Android 15 Easter Egg [Customized by Camila Foster, Sammy Fans]
Samsung Android 15 One UI 7 Ineligible Device List
The following is the list of Samsung devices that will not get the Android 15 One UI 7 update:
Galaxy A series
- Galaxy A04s
- Galaxy A13
- Galaxy A23
- Galaxy A72
- Galaxy A52
- Galaxy A52 5G
- Galaxy A52s
Galaxy M series
- Galaxy M53 5G
- Galaxy M33 5G
- Galaxy M23
Galaxy F series
- Galaxy F23
If you own any of these devices, you may want to consider upgrading to a newer model that will support One UI 7 and beyond.
Note: The list is compiled on software update policy and previous rollouts.