Android
Android 14 Beta 2 announced with plenty of bug fixes

Google starts rolling out the Android 14 Beta 2 update for testers using Pixel smartphones. As Samsung’s One UI 6 will be based on Android 14, the development progress and stability enhancements are necessary for a seamless and worry-free One UI Beta Program.
According to the information, Google’s Android 14 Beta 2 update adds support for built-in and custom predictive back animations. With the first Beta, the company introduced a new Back Arrow, which now gained support for predictive back animations.
Follow our socials → Google News, Telegram, Twitter, Facebook
Adding to this, the latest Beta firmware brings secure full-screen Intent notifications and makes data safety information more visible. Besides, there are a lot of issues been fixed that were reported by the developers’ community and end-users.
Stable Android 14 Release
Google has announced that the stable release of Android 14 is expected in August 2023. The first developer preview of Android 14 was released in February 2023, and subsequent beta releases have been released every few weeks. The final beta release is expected in July 2023, and the stable release will follow shortly after.
Android 14’s a big update for Samsung
Android 14 will bring a number of new features and improvements, including a new design language, privacy features, and performance improvements. Samsung has been working closely with Google to develop Android 14, and it is expected that the update will be well-integrated with its own software features.

What’s new in Android 14 Beta 2
Android 14 Beta 2 includes some new features and changes to try out:
- Add support for built-in and custom predictive back animations
- Secure full-screen Intent notifications
- Data safety information is more visible
Top resolved issues
The following issues have been resolved in Android 14 Beta 2:
Developer-reported issues
- Fixed a platform stability issue that could cause the UI to lag or freeze, apps to crash, or the device to crash.
- Fixed an issue with the fingerprint sensor that prevented new fingerprints from being added for Fingerprint Unlock in some cases.
- Fixed issues with UPI and biometrics that could cause some apps to not work properly.
- Fixed an issue where a device couldn’t be unlocked using a fingerprint after tapping a notification or choosing a notification action on the lock screen.
- Fixed an issue on some devices that caused sound to play through the speakers instead of headphones that were connected.
- Fixed an issue that caused icons on the home screen to appear almost invisible.
- Fixed issues with gesture navigation that occurred when using a custom launcher:
- The Home screen content wouldn’t display and the animation would fail to render when swiping up to go Home.
- The list of recently used apps couldn’t be accessed using the normal gesture.
- Fixed issues that prevented users from interacting with notifications in the notification shade.
- Fixed an issue that could cause a device to crash after finishing audio or video calls.
Other resolved issues
- Fixed an issue where, after entering and exiting picture-in-picture mode, the screen flickered when any apps were launched.
- Fixed an issue where user restrictions set by DPC admins were not being enforced in Settings.
- Fixed an issue where, after taking pictures with the Google Camera app, opening the latest picture from the thumbnail in the app briefly displayed a green-colored shade over the image.
- Fixed an issue that could cause the battery percentage to be displayed as 0% after a device reboot regardless of the actual charge level of the device.
- Fixed an issue that could cause a device to crash, and then when the device rebooted any wallpapers that were selected before the reboot were reset.
- Fixed issues that prevented the Better Bug app from uploading bug reports.
- Fixed issues that caused the back-to-home gesture to stop working.
- Fixed an issue that could cause the system Settings app to crash repeatedly.
- Fixed an issue that prevented users from searching within the system Settings app.
- Fixed issues that sometimes caused null pointer exceptions for input method editors (IMEs).
- Fixed an issue that sometimes increased system-wide memory usage unnecessarily.
- Fixed system issues that could sometimes cause deadlocks.
| Source |
Android
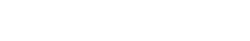
One UI 7 to bring Android 15’s secret Landroid screensaver

Android 15’s Easter Egg includes a secret Landroid screensaver mode that One UI 7 might borrow. Samsung’s next One UI iteration will be based on Android 15 OS. Core Android features such as Easter Egg will be included in Galaxy’s next major upgrade.
Debuted as a Landroid screensaver, Android 15’s Easter egg was added with the latest Beta. Google News Telegram channel’s Nail Sadykov discovered that the Easter egg game is equipped with an integrated screensaver mode.
To activate Easter Egg, head into Settings followed by About phone and Android version. Once done, tap the displayed Android version several times until you see the Android 15 bugdroid logo floating in space.
Space travel mini-game will be available to play added with Android 14. When you initially trigger the mini-game, you should have unlocked the new screensaver, tucked away under Settings → Display & Touch → Screen saver → Landroid.
After activating the screensaver, you can set your phone on your desk. Now, the phone will let you watch the Easter egg game take over in autopilot mode, as the spacecraft automatically dodges planets – it provides a better experience on a tablet placed on a dock.
AI
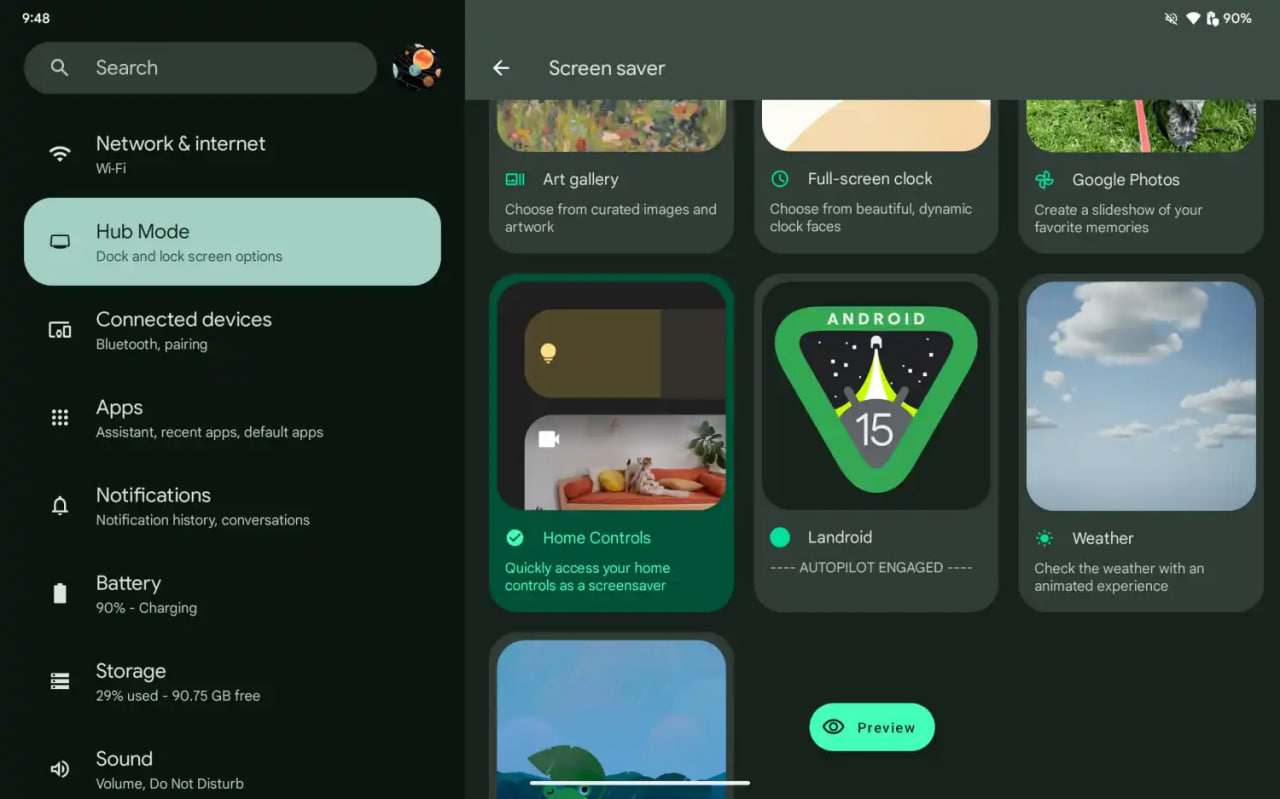
Android 15 might let you share AI-generated wallpapers

Google introduced the AI Wallpaper feature with the Pixel 8 series. The same functionality is also available in Samsung’s Galaxy S24 series thanks to Genini Nano. Now, Google is preparing to make AI-generated wallpapers sharable with Android 15.
Pixel’s ability to create AI-generated wallpapers is quite popular among users. Currently, the feature only allows users to generate stunning wallpapers and apply on the home screen and lock screen. Sharing with someone presently requires to be saved as a screenshot.
Threads user @the_husbandalorian discovered interesting evidence in the latest Beta. The company is working on a new option in Android 15 to share AI-generated wallpapers. A new share button is added on the preview screen in the wallpaper picker interface.
Post by @the_husbandalorianView on Threads
The preview will display how the wallpaper will be applied to your phone’s home or lock screen. The pencil button will allow you to refine the prompt used to create the wallpaper. Share button is all you need to share AI-generated wallpaper with others.
At present, the ability to share AI-generated wallpaper is broken. It suggests the feature is still under development and requires additional work. The next Beta might make it functional for Beta users, and we guess public availability with a Stable rollout.
AI Wallpaper in One UI 6.1
Android
Samsung Android 15 Update: One UI 7 Ineligible Devices [LIST]

Samsung is very well known for its excellent after-sales service and software support. The company announced that it will provide up to 7 years of major OS upgrades and security updates for its flagship devices, starting with the Galaxy S24 series. This is a remarkable achievement that will allow Samsung users to enjoy the latest features and security enhancements for a long time.
Not all Samsung devices will be eligible for the upcoming Android 15-based One UI 7 update, which is expected to bring several new features and improvements. Some older and lower-end models of the Galaxy A, Galaxy M, and Galaxy F series have reached the end of their software upgrade cycles, and will not receive any further OS updates.
Follow our socials → Google News, Telegram, X (formerly Twitter), Facebook
However, these devices will still receive security patches for another year, but they will miss out on the new features and benefits of One UI 7.

Android 15 Easter Egg [Customized by Camila Foster, Sammy Fans]
Samsung Android 15 One UI 7 Ineligible Device List
The following is the list of Samsung devices that will not get the Android 15 One UI 7 update:
Galaxy A series
- Galaxy A04s
- Galaxy A13
- Galaxy A23
- Galaxy A72
- Galaxy A52
- Galaxy A52 5G
- Galaxy A52s
Galaxy M series
- Galaxy M53 5G
- Galaxy M33 5G
- Galaxy M23
Galaxy F series
- Galaxy F23
If you own any of these devices, you may want to consider upgrading to a newer model that will support One UI 7 and beyond.
Note: The list is compiled on software update policy and previous rollouts.